A phishing email is a type of social engineering attack where cyber criminals will trick victims into handing over sensitive information or installing malware. Phishing, pronounced ‘fishing’, is one of the most common types of cybercrime. Even if we know everything about phishing emails, people still frequently fall victim to their attacks.
1. Public Email Domains
Every business will have their own email domain, except possibly one-man bands. No legitimate company will use a public email domain like ‘@gmail.com’. It would always include their company name after the @ symbol like so: @cambridgesupport.com.
Therefore, when receiving an email that looks suspicious, don’t rely on the contact’s name, click on their name to show their actual email. This will reveal all. As you can see below, the email domain should be @paypal.com, but it’s not.
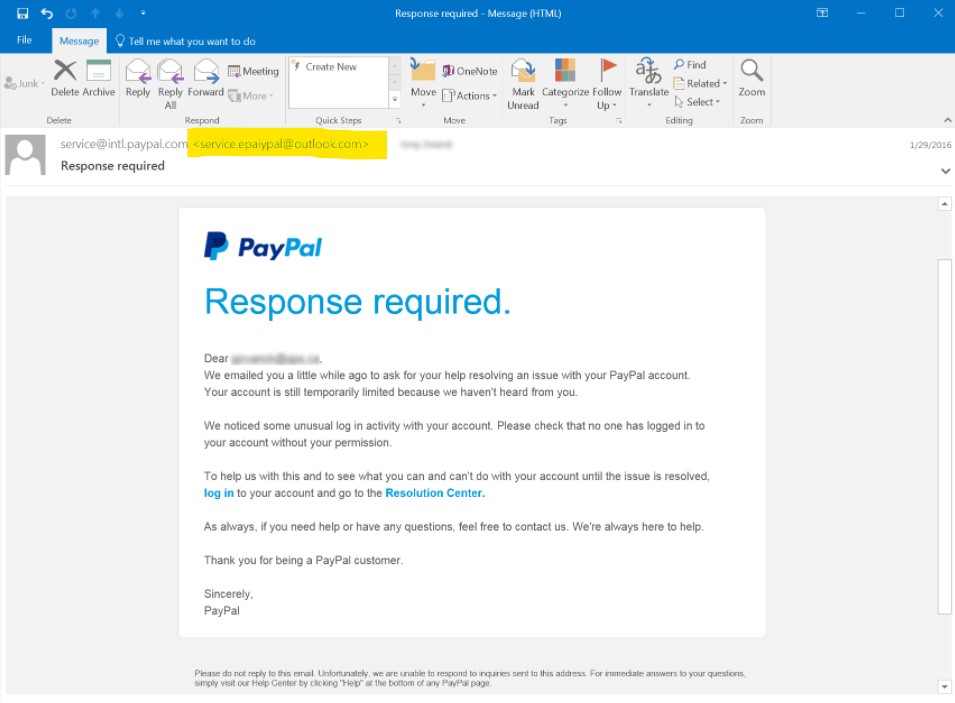
You will notice that in this email, part of the company name is in the email. This is a more sophisticated approach. However, one must always remember that the company name must come after the @ symbol and that it must be spelt correctly. Any email from a public domain name like Gmail or Outlook, could be a scam.
2. Misspelling of the Domain Name
As mentioned above, scammers are clever. They will create new domain names which look very similar to the company domain. If we take the example of eBay. The scammers domain name would be similar, but not the same. Scammers could use ‘@elbay.com’ with an extra ‘L’ in the middle. This could potentially catch many people off guard. Sometimes it can only be a letter missing or replace a letter with a number.
3. It Looks Like a Contact of Yours
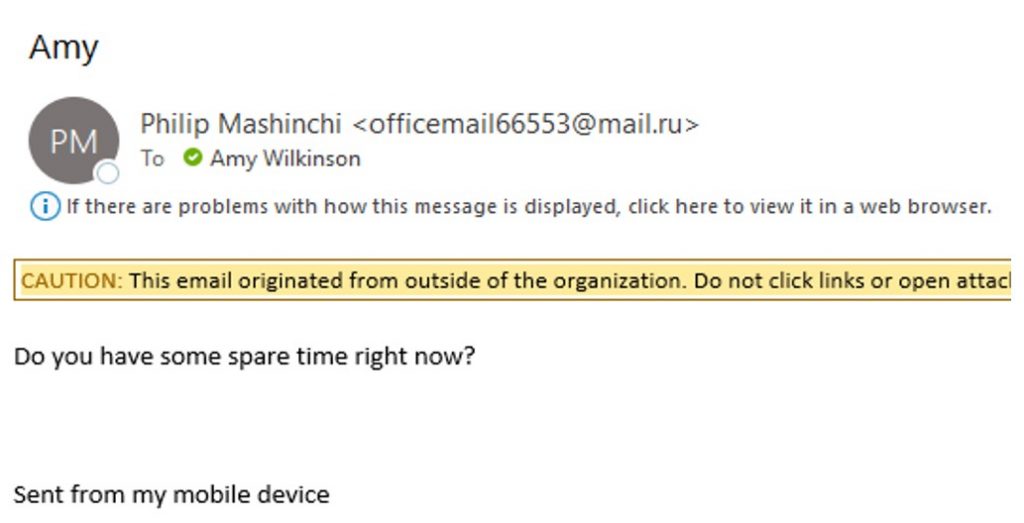
Often, phishing emails appear as if it’s originated from a contact of yours. Meaning that their name is identical to your contact, but its not really your contact. If you see the image below, this is a good example. The contact’s name is perfect, but the email is not. For some email providers, you may need to click on the contacts name to see their email. Its only by seeing the email domain that you can distinguish whether its genuine or not.
4. Poorly Written Email
A phishing email may contain poor spelling and/or poor grammar. When composing emails, scammers where their native language is not English will often use a spellchecker or translation machine. This will provide the right words but not necessarily in the right context. In addition, if the email is received from a friend or work colleague, you will know their writing style. Therefore, based on previous interactions with them you will be familiar with their choice of words they may or may not use.
5. Suspicious Links or Attachments
A phishing emails purpose is to trick victims into handing over sensitive information or installing malware through a link or an attachment.
A suspicious link is a common means to obtain sensitive data. Typically, the hacker will impersonate a well known company like PayPal or Microsoft, state an urgent problem and ask you to sign in to prevent further damage. It is at this point where the user has just handed over all their information to the scammer, unknowingly.
An infected attachment can often come in the form of an invoice. If the user clicks on the attachment, it will open malware on the device. This then has the potential to spread across the whole company. If you are not sure, don’t open the attachment. The best thing is to double check by phoning the person who sent it.
Most of these emails commonly have a sense of urgency, which causes the user to act quickly without properly thinking things through.
6. Check Warning Banners on the Email
Typically, if you have some form of spam filtering, then a notification banner is usually present at the top informing you it’s from ‘outside your organisation’ or ‘you don’t often get an email from …’. Always pay attention to these and proceed with caution.


Overall, if you are ever in doubt, its best to double check with the sender in which the email is trying to impersonate. Best to do this by face to face, by phone or in a new email.
Are You Phishing For IT Support?
Cambridge Support is an award-winning IT company in Cambridgeshire. We love helping companies manage their IT systems. We have a vast amount of experience in a range of security focused services. Cambridge Support also offer security audits, Cyber Essentials, and Microsoft 365 audits.
If you have any phishing email issues or anything security related, please contact us today. We would love to hear from you and will be more than happy to discuss any concerns you have. For more information please contact us on 01223 921 000, or you can email at ask@cambridgesupport.com.